Challenge Brigitte Friang - Entry
Challenge Brigitte Friang write-up
Organized by the DGSE and ESIEE Paris
Website link: https://challengecybersec.fr
(It might not work anymore)
We only had this website, because this is where it all starts.
Source code of the web page (ctrl+u) :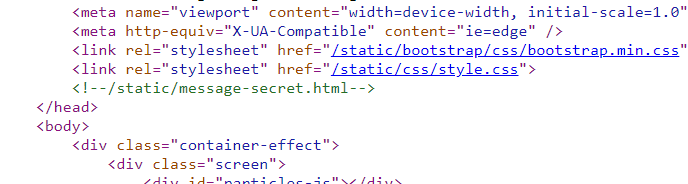
We can clearly see that there’s a hidden link.
On this hidden link, /static/message-secret.html is a secret message.
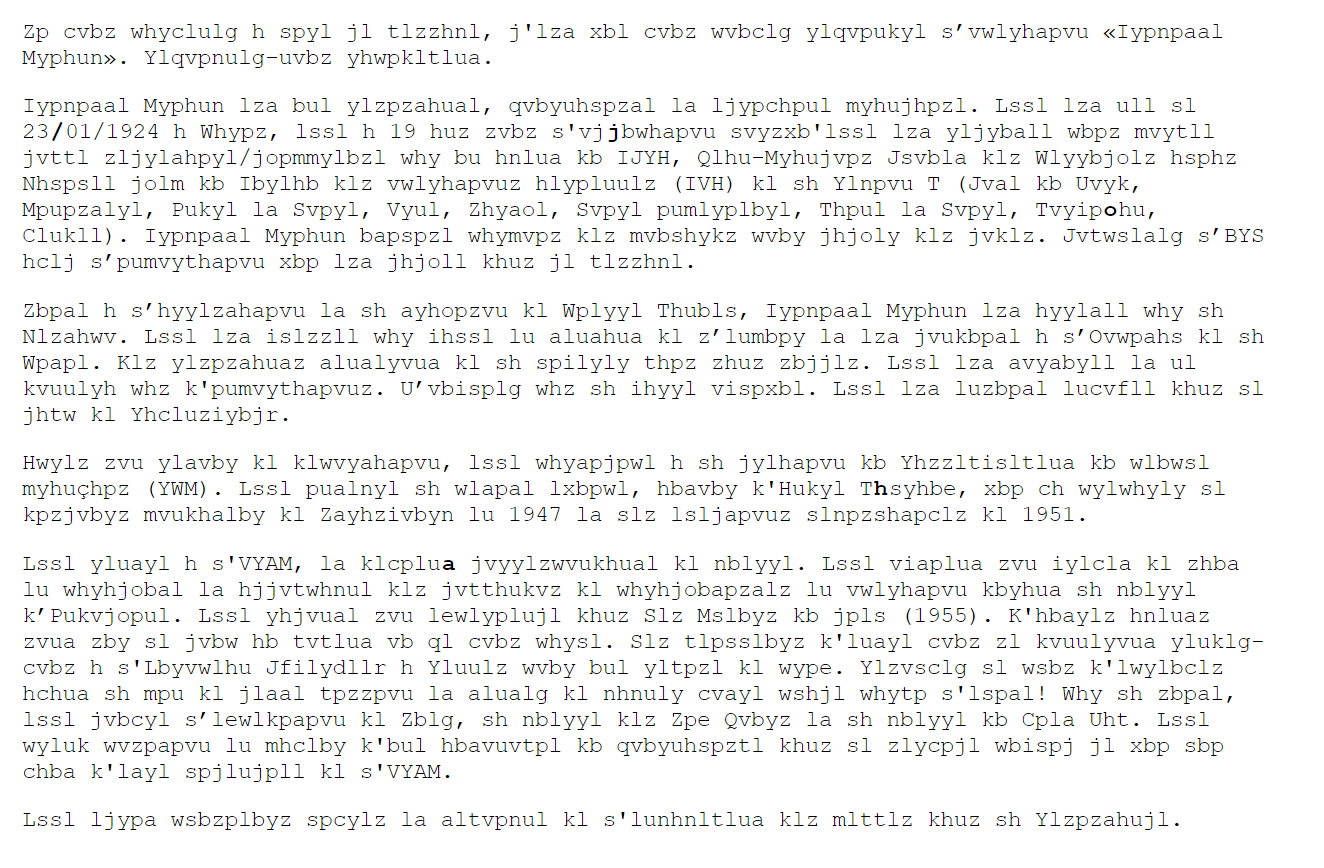
Caesar
Zp cvbz whyclulg h spyl jl tlzzhnl, j'lza xbl cvbz wvbclg ylqvpukyl svwlyhapvu Iypnpaal Myphun. Ylqvpnulg-uvbz yhwpkltlua.
Iypnpaal Myphun lza bul ylzpzahual, qvbyuhspzal la ljypchpul myhujhpzl. Lssl lza ull sl 23/01/1924 h Whypz, lssl h 19 huz zvbz s'vjjbwhapvu svyzxb'lssl lza yljyball wbpz mvytll jvttl zljylahpyl/jopmmylbzl why bu hnlua kb IJYH, Qlhu-Myhujvpz Jsvbla klz Wlyybjolz hsphz Nhspsll jolm kb Ibylhb klz vwlyhapvuz hlypluulz (IVH) kl sh Ylnpvu T (Jval kb Uvyk, Mpupzalyl, Pukyl la Svpyl, Vyul, Zhyaol, Svpyl pumlyplbyl, Thpul la Svpyl, Tvyipohu, Clukll). Iypnpaal Myphun bapspzl whymvpz klz mvbshykz wvby jhjoly klz jvklz. Jvtwslalg sBYS hclj spumvythapvu xbp lza jhjoll khuz jl tlzzhnl.
Zbpal h shyylzahapvu la sh ayhopzvu kl Wplyyl Thubls, Iypnpaal Myphun lza hyylall why sh Nlzahwv. Lssl lza islzzll why ihssl lu aluahua kl zlumbpy la lza jvukbpal h sOvwpahs kl sh Wpapl. Klz ylzpzahuaz alualyvua kl sh spilyly thpz zhuz zbjjlz. Lssl lza avyabyll la ul kvuulyh whz k'pumvythapvuz. Uvbisplg whz sh ihyyl vispxbl. Lssl lza luzbpal lucvfll khuz sl jhtw kl Yhcluziybjr.
Hwylz zvu ylavby kl klwvyahapvu, lssl whyapjpwl h sh jylhapvu kb Yhzzltisltlua kb wlbwsl myhuçhpz (YWM). Lssl pualnyl sh wlapal lxbpwl, hbavby k'Hukyl Thsyhbe, xbp ch wylwhyly sl kpzjvbyz mvukhalby kl Zayhzivbyn lu 1947 la slz lsljapvuz slnpzshapclz kl 1951.
Lssl yluayl h s'VYAM, la klcplua jvyylzwvukhual kl nblyyl. Lssl viaplua zvu iylcla kl zhba lu whyhjobal la hjjvtwhnul klz jvtthukvz kl whyhjobapzalz lu vwlyhapvu kbyhua sh nblyyl kPukvjopul. Lssl yhjvual zvu lewlyplujl khuz Slz Mslbyz kb jpls (1955). K'hbaylz hnluaz zvua zby sl jvbw hb tvtlua vb ql cvbz whysl. Slz tlpsslbyz k'luayl cvbz zl kvuulyvua yluklg-cvbz h s'Lbyvwlhu Jfilydllr h Yluulz wvby bul yltpzl kl wype. Ylzvsclg sl wsbz k'lwylbclz hchua sh mpu kl jlaal tpzzpvu la alualg kl nhnuly cvayl wshjl whytp s'lspal! Why sh zbpal, lssl jvbcyl slewlkpapvu kl Zblg, sh nblyyl klz Zpe Qvbyz la sh nblyyl kb Cpla Uht. Lssl wyluk wvzpapvu lu mhclby k'bul hbavuvtpl kb qvbyuhspztl khuz sl zlycpjl wbispj jl xbp sbp chba k'layl spjlujpll kl s'VYAM.
Lssl ljypa wsbzplbyz spcylz la altvpnul kl s'lunhnltlua klz mlttlz khuz sh Ylzpzahujl.The title of that page is “caesar”, so I went to cyberchef and used ROT13 to decode the message. I tried all the alterations until I found something relevant. And I had to use 19 alterations to find a correct message.
Si vous parvenez a lire ce message, c'est que vous pouvez rejoindre loperation Brigitte Friang. Rejoignez-nous rapidement.
Brigitte Friang est une resistante, journaliste et ecrivaine francaise. Elle est nee le 23/01/1924 a Paris, elle a 19 ans sous l'occupation lorsqu'elle est recrutee puis formee comme secretaire/chiffreuse par un agent du BCRA, Jean-Francois Clouet des Perruches alias Galilee chef du Bureau des operations aeriennes (BOA) de la Region M (Cote du Nord, Finistere, Indre et Loire, Orne, Sarthe, Loire inferieure, Maine et Loire, Morbihan, Vendee). Brigitte Friang utilise parfois des foulards pour cacher des codes. Completez lURL avec linformation qui est cachee dans ce message.
Suite a larrestation et la trahison de Pierre Manuel, Brigitte Friang est arretee par la Gestapo. Elle est blessee par balle en tentant de senfuir et est conduite a lHopital de la Pitie. Des resistants tenteront de la liberer mais sans succes. Elle est torturee et ne donnera pas d'informations. Noubliez pas la barre oblique. Elle est ensuite envoyee dans le camp de Ravensbruck.
Apres son retour de deportation, elle participe a la creation du Rassemblement du peuple français (RPF). Elle integre la petite equipe, autour d'Andre Malraux, qui va preparer le discours fondateur de Strasbourg en 1947 et les elections legislatives de 1951.
Elle rentre a l'ORTF, et devient correspondante de guerre. Elle obtient son brevet de saut en parachute et accompagne des commandos de parachutistes en operation durant la guerre dIndochine. Elle raconte son experience dans Les Fleurs du ciel (1955). D'autres agents sont sur le coup au moment ou je vous parle. Les meilleurs d'entre vous se donneront rendez-vous a l'European Cyberweek a Rennes pour une remise de prix. Resolvez le plus d'epreuves avant la fin de cette mission et tentez de gagner votre place parmi l'elite! Par la suite, elle couvre lexpedition de Suez, la guerre des Six Jours et la guerre du Viet Nam. Elle prend position en faveur d'une autonomie du journalisme dans le service public ce qui lui vaut d'etre licenciee de l'ORTF.
Elle ecrit plusieurs livres et temoigne de l'engagement des femmes dans la Resistance.There is another hidden message, indeed on the “message-secret.html” page we can see that some characters are in bold :
We got this word:/joha
And, of course we have to use caesar encryption on it such as on the whole text. And we got /chat.
Chatroom
Completing the domain with that location, (challengecybersec.fr/chat), opens something like a chatroom :

There are messages with other people, such as “Armand Richelieu”, “Antoine Rossignol” or “Jérémy Nitel”.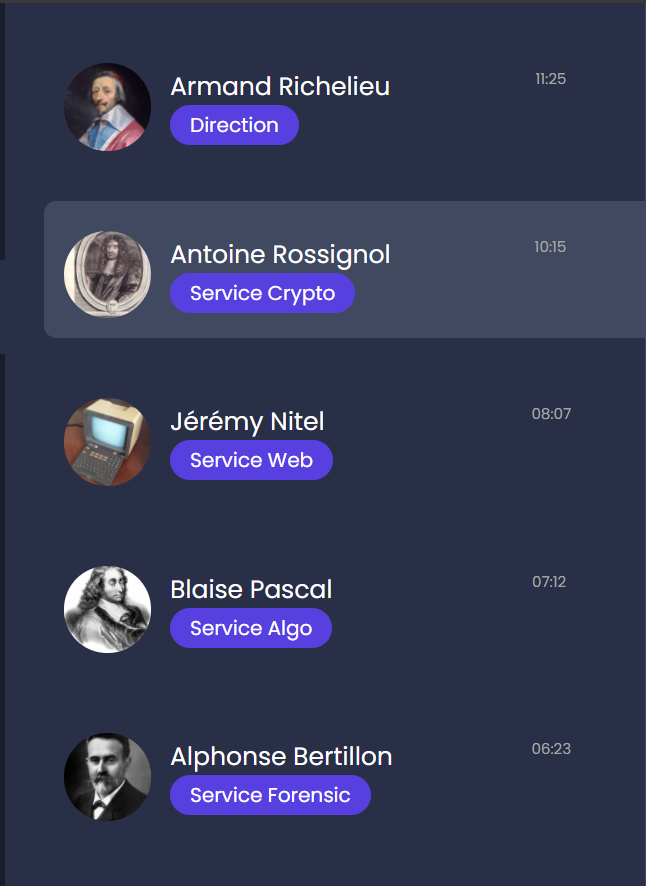
From here we can choose one of the paths to get an entrance ticket.
But that, I didn’t know it yet. That was the easy part.
I tried to go through all the paths, but I only had the time to do two of them.
Antoine Rossignol - Cryptography
Let’s begin with Antoine Rossignol’s cryptography challenge.
Antoine Rossignol provided me some text files, encrypted files and pdf’s.
I have to discorver what’s inside “archive_chiffree”.
The conversation:
Antoine Rossignol 29/09/2020 : "Un des nos agents a intercepté du matériel de chiffrement et un message chiffré émis par Evil Chems qui doit contenir des informations capitales sur la livraison de produits chimiques."
Agent 40 30/09/2020 : "OK, on s'occupe de démonter le matériel pour analyse."
Agent 40 08/10/2020 : "C'est plus compliqué que prévu! Le processeur ne fait qu'échanger des données avec un circuit intégré dédié (ASIC). On suppose qu'il contient l'algorithme de chiffrement et que la clé y est stockée en dur."
Antoine Rossignol 08/10/2020 : " Envoyez en urgence l'ASIC à Eve Descartes d'ESIEE-Paris pour une rétro-conception matérielle"
Agent 40 12/10/2020 : "Eve Descartes a bien reçu le circuit. Elle s'en occupe en priorité."
Antoine Rossignol 23/10/2020 : "Voici le compte-rendu d'Eve avec la cartographie de la zone étudiée. Il devient urgent de déchiffrer le message."As I said I was given two PDF files, but Layout.pdf was protected with a password.
And here’s the other one:
The most important informations were that theyachieved to do some hardware reverse engineering on the microchip. There semm to be two different areas, one which we can’t see which is probably the encryption key, and the other one should be the algorithm for that key, which we can see.
The algorithm is probably a well known standard encryption method.
They detected 256 programmable eFuses.
And they aren’t sure about the bit order and the MSB position.
Eve also said that we can contact her if we have an issue.
She didn’t send me the password. So I called Her.
Also, sending her an email tells us to call her.
And the answer was some morse :
Which gives me .-. . ... .. ... - .- -. -.-. .
The first letter wasn’t audible, but I found out that the passwod was resistance.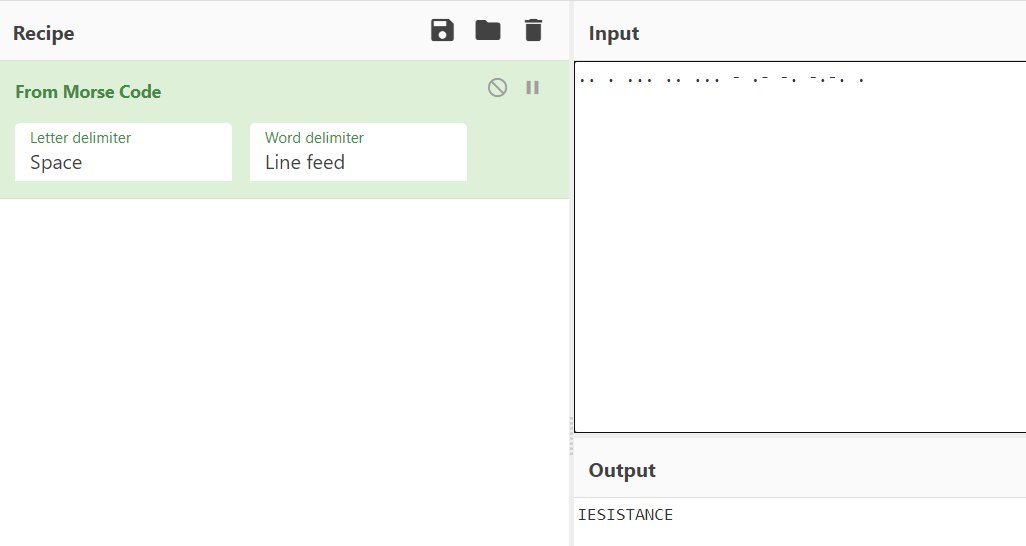
In the protected PDF we can see that picture:
Which are clearly looking like fuses. Remember, eFuses !
There are exactly 256.
In computing, eFuse is a technology invented by IBM which allows for the dynamic real-time reprogramming of computer chips. In the abstract, computer logic is generally “etched” or “hard-coded” onto a chip and cannot be changed after the chip has finished being manufactured. - Wikipedia
I immediately thought about binary when I saw that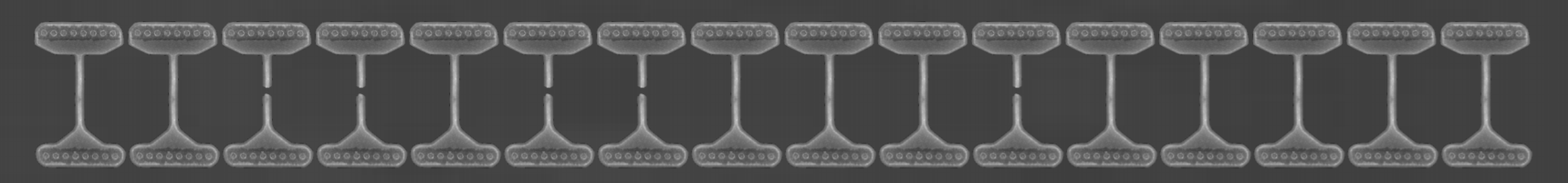
I thought that 0 was for cutted fuse and 1 for non-cutted. That gave me this :
1011111010111010101011001101111111001101110010101100100111011111101110101011110010111101110111111101111111011111110111111101111111011111110111111101111111011111110111111101111111011111110111111101111111011111110111111101111111011111110111111101111111011111But I had to flip the bits, to get something like this :
010000010100010101010011001000000110010001101010011011000100000010001010100001101000010001000000010000000100000001000000010000000100000001000000010000000100000001000000010000000100000001000000010000000100000001000000010000000100000001000000010000000100000Which meansAES 256 ECB 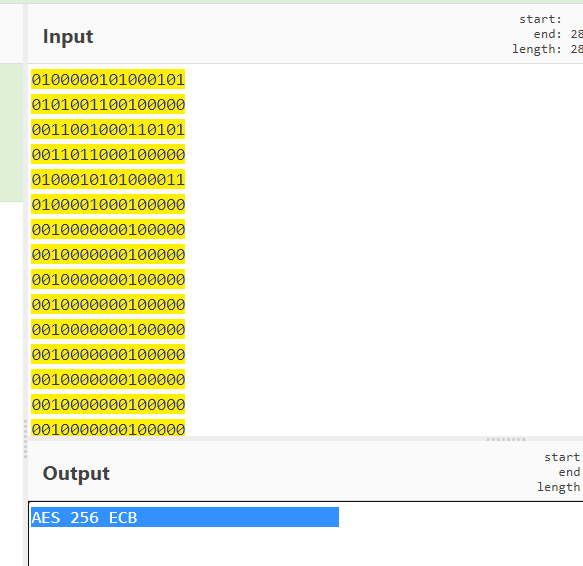
Notice the lenght, it's very important
Now, I have all the informations to decrypt the file.
On cyberchef I used the following parameters:
KEY(utf8): AES 256 ECB (notice the spaces, the key have to be 32 bytes long)
IV: Nothing
Mode: ECB
Input: Raw
Output: Raw
GCM Tag: Nothing
On my first try I copy/pasted the file content into cyberchef. But it didn’t work so I opened the file as input.
And then I got an output: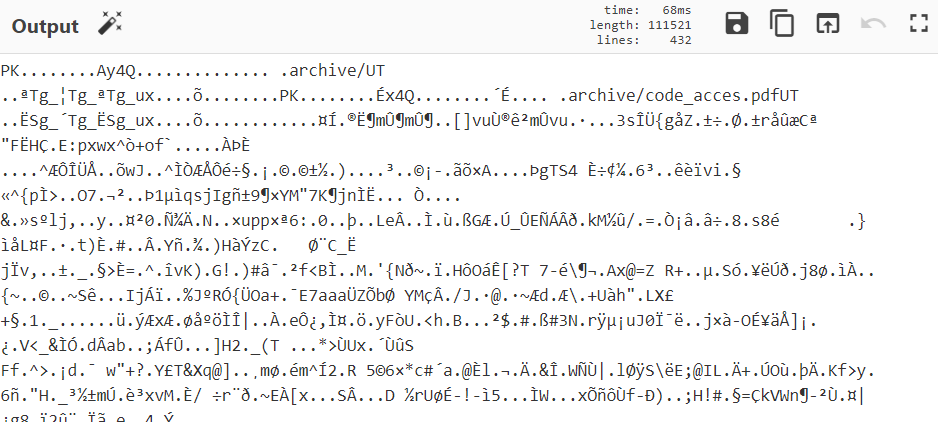
This is a ZIP file, so I saved the output to a file with the .zip extension.
And here it is :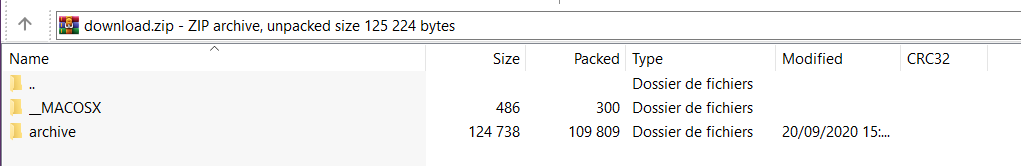
There is a password protected PDF and a message from Evil Chems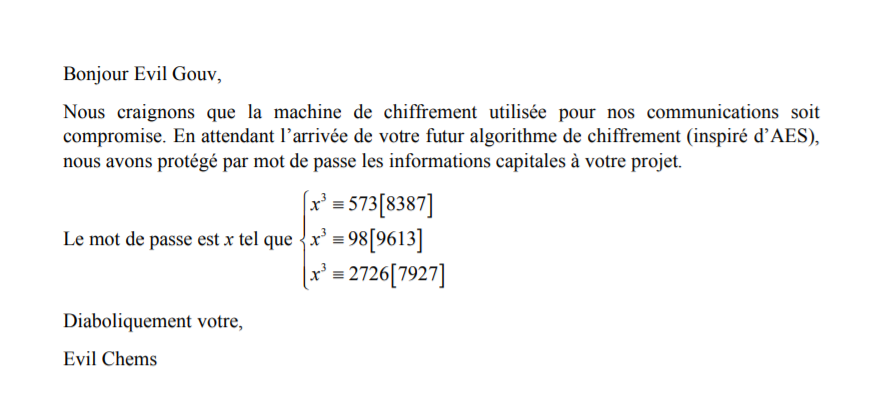
Oh god… it probably means that I have to do maths…
(Yeah, cryptography)
After I watched nearly one hour of math videos about congruence, and I finally discovered how it works.
And I used dcode’s modular equation calculator to do it with big numbers.
https://www.dcode.fr/modular-equation-solver
x 573[8387] (Result is x = 5622)
x 98[9613] (Results are x = 5622 OR x = 5964 OR x = 7640)
x 2726[7927] (Results are x = 2589 OR x = 5622 OR x = 7643)
The result 5622 appears each time, so I can assume that this is the password. And it was.
The password for the protected PDF was 5622.
Now we have this message: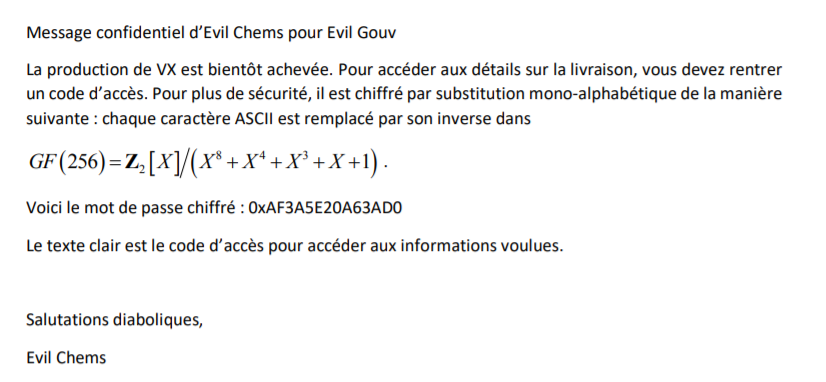
And.. yeah, maths, again.
This time, what is used is called Galois Field (GF(256)), also called finite field.
I won’t go into the details, because I could make a lot of mistakes…
Howewer, this is widely used in cryptography and all I can say, is that this is used by AES encryption.
We also have a encrypted password (0xAF3A5E20A63AD0), this password has 7 bytes (AF 3A 5E 20 A6 3A D0) and when I convert that with a multiplicative inverse table, it gives me something like this:
62 20 61 3A 65 20 7A
Here’s the table I used:
| Table of multiplicative inverses: rs*inv(rs) = 01 | |||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| inv(rs) | s | ||||||||||||||||
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | a | b | c | d | e | f | ||
| r | |||||||||||||||||
| 0 | XX | 01 | 8d | f6 | cb | 52 | 7b | d1 | e8 | 4f | 29 | c0 | b0 | e1 | e5 | c7 | |
| 1 | 74 | b4 | aa | 4b | 99 | 2b | 60 | 5f | 58 | 3f | fd | cc | ff | 40 | ee | b2 | |
| 2 | 3a | 6e | 5a | f1 | 55 | 4d | a8 | c9 | c1 | 0a | 98 | 15 | 30 | 44 | a2 | c2 | |
| 3 | 2c | 45 | 92 | 6c | f3 | 39 | 66 | 42 | f2 | 35 | 20 | 6f | 77 | bb | 59 | 19 | |
| 4 | 1d | fe | 37 | 67 | 2d | 31 | f5 | 69 | a7 | 64 | ab | 13 | 54 | 25 | e9 | 09 | |
| 5 | ed | 5c | 05 | ca | 4c | 24 | 87 | bf | 18 | 3e | 22 | f0 | 51 | ec | 61 | 17 | |
| 6 | 16 | 5e | af | d3 | 49 | a6 | 36 | 43 | f4 | 47 | 91 | df | 33 | 93 | 21 | 3b | |
| 7 | 79 | b7 | 97 | 85 | 10 | b5 | ba | 3c | b6 | 70 | d0 | 06 | a1 | fa | 81 | 82 | |
| 8 | 83 | 7e | 7f | 80 | 96 | 73 | be | 56 | 9b | 9e | 95 | d9 | f7 | 02 | b9 | a4 | |
| 9 | de | 6a | 32 | 6d | d8 | 8a | 84 | 72 | 2a | 14 | 9f | 88 | f9 | dc | 89 | 9a | |
| a | fb | 7c | 2e | c3 | 8f | b8 | 65 | 48 | 26 | c8 | 12 | 4a | ce | e7 | d2 | 62 | |
| b | 0c | e0 | 1f | ef | 11 | 75 | 78 | 71 | a5 | 8e | 76 | 3d | bd | bc | 86 | 57 | |
| c | 0b | 28 | 2f | a3 | da | d4 | e4 | 0f | a9 | 27 | 53 | 04 | 1b | fc | ac | e6 | |
| d | 7a | 07 | ae | 63 | c5 | db | e2 | ea | 94 | 8b | c4 | d5 | 9d | f8 | 90 | 6b | |
| e | b1 | 0d | d6 | eb | c6 | 0e | cf | ad | 08 | 4e | d7 | e3 | 5d | 50 | 1e | b3 | |
| f | 5b | 23 | 38 | 34 | 68 | 46 | 03 | 8c | dd | 9c | 7d | a0 | cd | 1a | 41 | 1c | |
Here’s an example for the first byte, how I found its multiplicative inverse: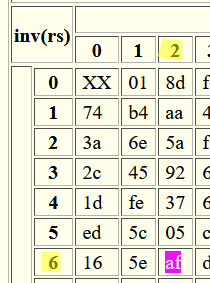
Now I have to decode these bytes to ASCII:
62 -> b
20 -> space
61 -> a
3A -> :
65 -> e
20 -> space
7A -> z
The password seemed to be b a:e z so I sent that to Antoine Rossignol.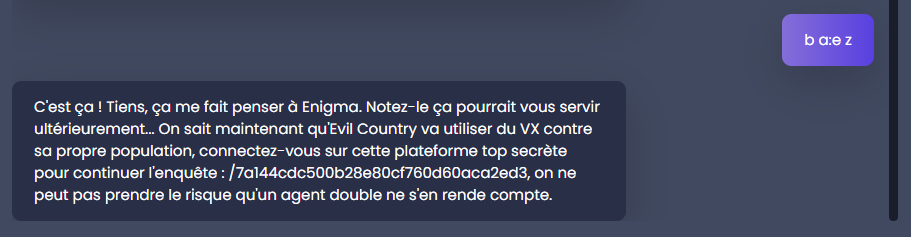
And I was correct !
And this directory is the final step to access the real CTF.
And that’s how I got my second entry ticket !
Jeremy Nitel - Web
This time I’m gonna attack the web challenge.
Stockos, a storage service is suspected to be a transit point for ware linked to a massacre of resistance fighters.
And apparently the credentials are extremely weak.
So, I tried admin:admin and I was in.
I had to perform an SQL injection on the stock page.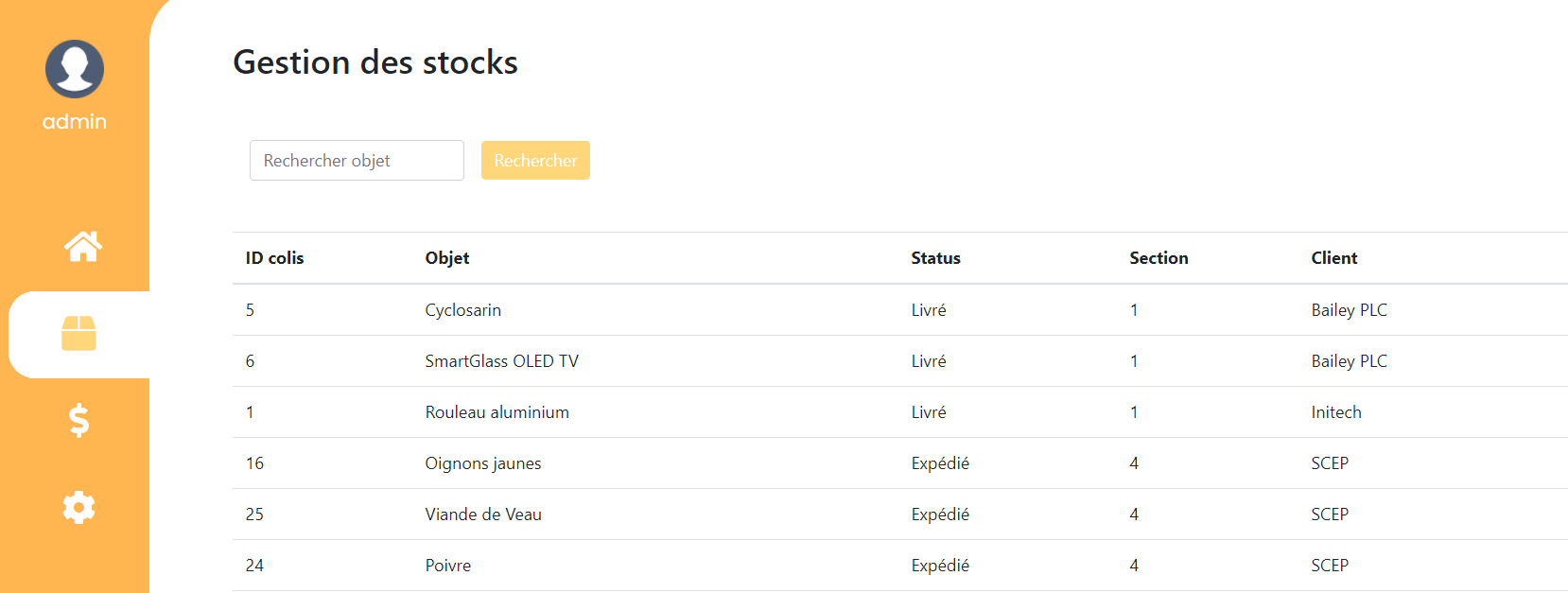
With this SQL command I could find Evil Gouv’s email address1' UNION SELECT id, name, email, 1, 1 FROM stockos.customer #
I learned a lot about SQL injections with this.
Which is 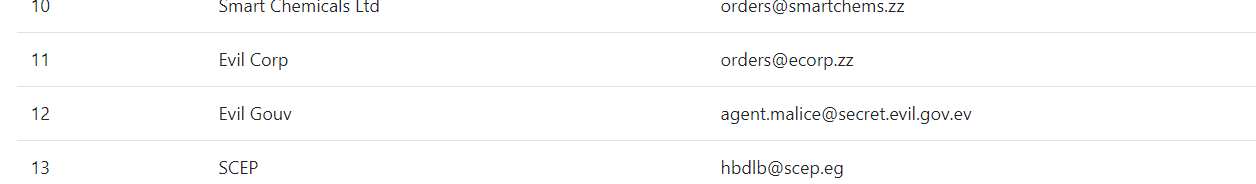
agent.malice@secret.evil.gov.ev
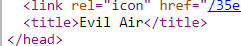
Then it was told me to book a flight on evil air’s website:
https://www.challengecybersec.fr/35e334a1ef338faf064da9eb5f861d3c/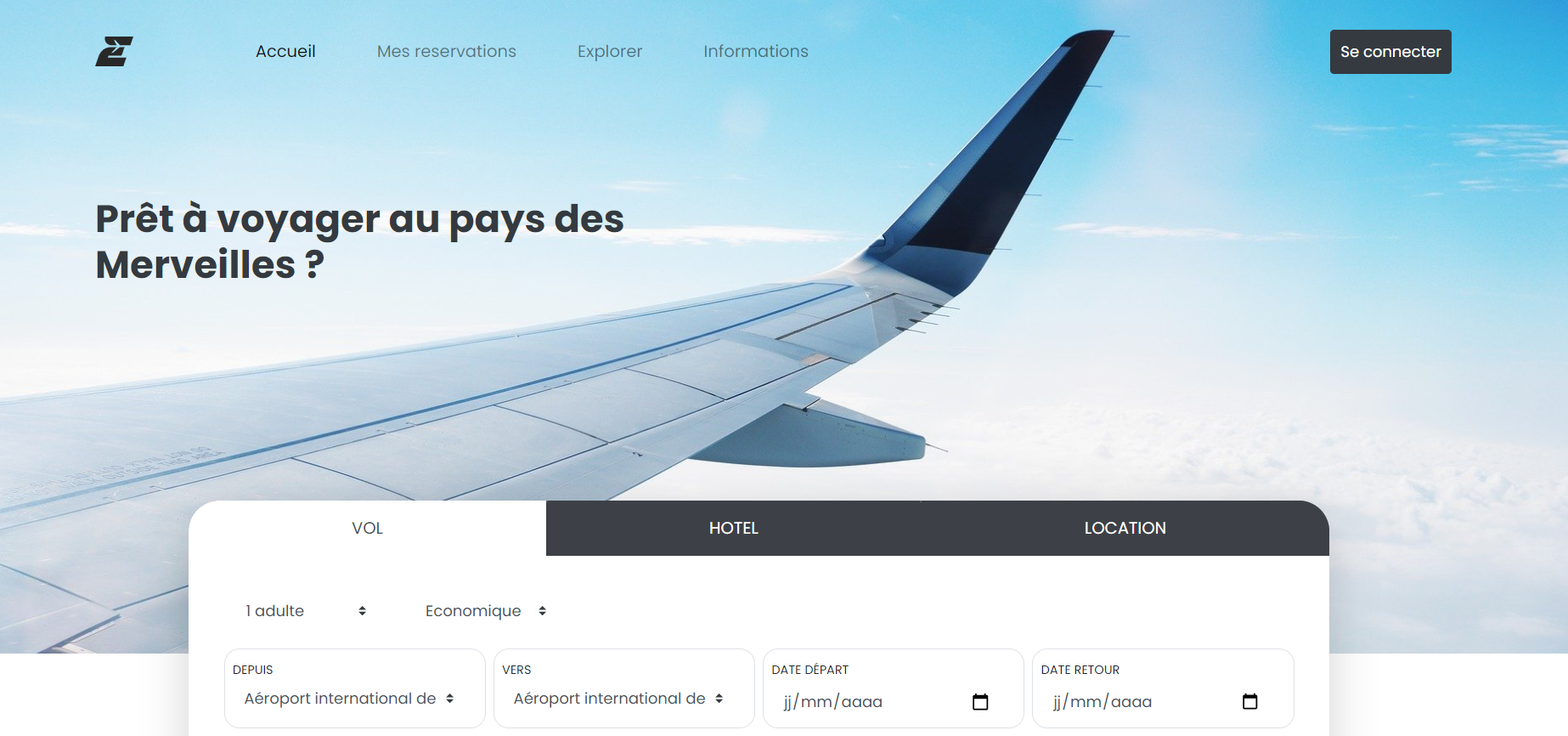
The flight is called ABDJI6
And it have to be from 26/10/2020 to 28/10/2020
From Bad City to Evil City
And… I should think about taking sunscreen, because the sun is beating down there.. hmm
Probably because it’s evil.
I created an account (I was warned to not use my usual credentials, and use a tempmail), with these informations:
name: ninja
mail: ninja@ninjamail.xyz
password: BFSRpx!4E…
Here’s the confirmation email they send me: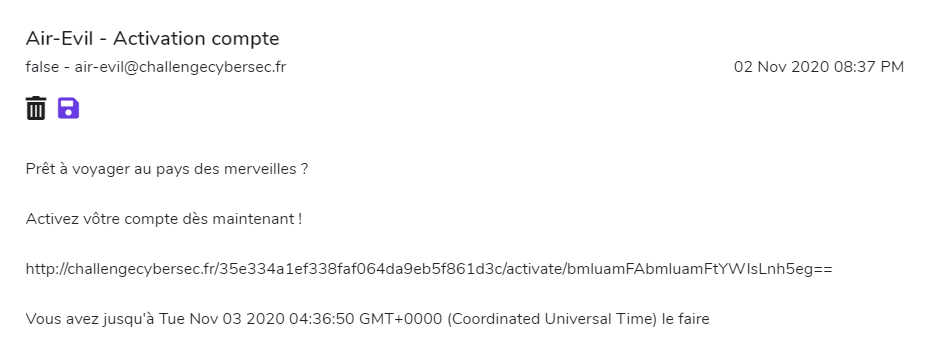
Prêt à voyager au pays des merveilles ?
Activez vôtre compte dès maintenant !
http://challengecybersec.fr/35e334a1ef338faf064da9eb5f861d3c/activate/bmluamFAbmluamFtYWlsLnh5eg==
Vous avez jusqu’à Tue Nov 03 2020 04:36:50 GMT+0000 (Coordinated Universal Time) le faire
Looks like a phishing mail lol:
Anyway,
The generated link basically just activated my account.
And the base64 is the email address I used, encoded in base64.
hmmm
Okay, let’s book that flight.
(I wanted a flight in business class, but unfortunately they didn’t take it into consideration…)
And I couldn’t book that destination.
On my profile page they said that I don’t have an “Authorized profile”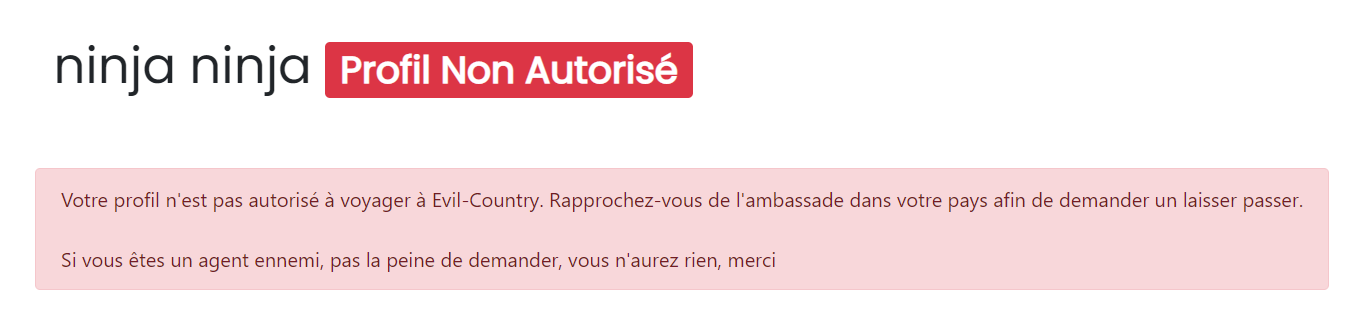
That’s not nice… let’s see the cookies.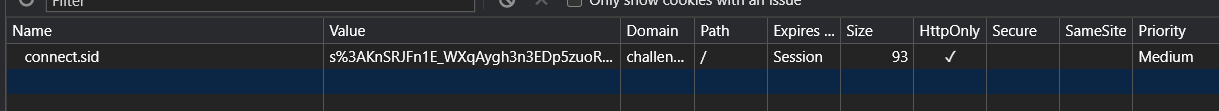
Nothing really interesting.
Okay, then I thought I had to extract the password from agent.malice
Because they warned me that the informations are in clear in the database.
But I found nothing.
Then, I decided to use the password recovery function of the website. They send me a recovery link, which contains my email in base64.
This is very similar to the activation link.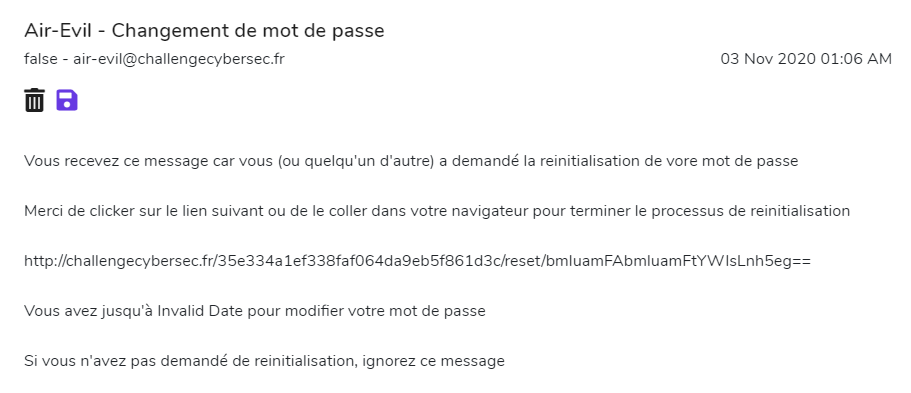
And, this link gives me my password in clear text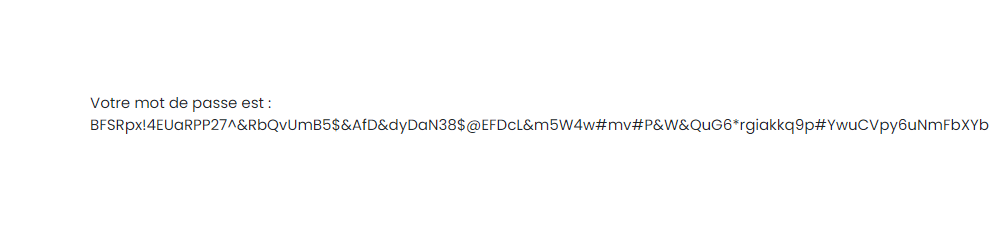
I tried to do the same thing with agent malice’s email address, I converted his email to base64 and replaced my token with that.
And it shows up the following password:
Superlongpassword666
I’m now authorized :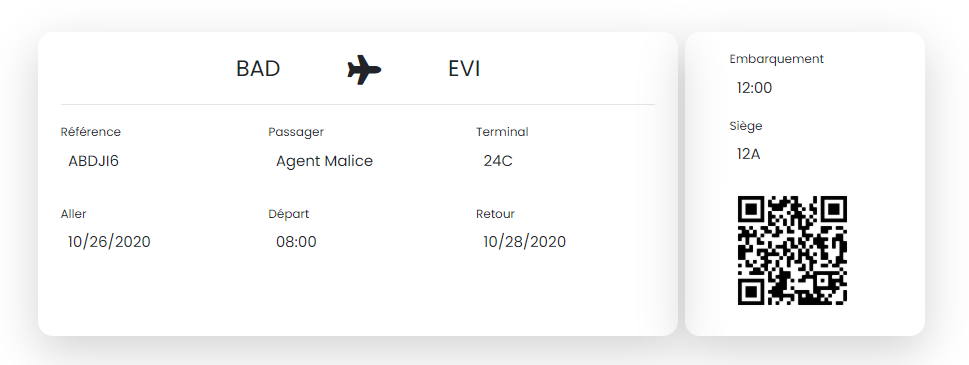
And I can see my flight at “bookings”
The QR Code gives me the flag:
DGSESIEE{2cd992f9b2319860ce3a35db6673a9b8}
And when I send it to Jérémy, he gave me another mission.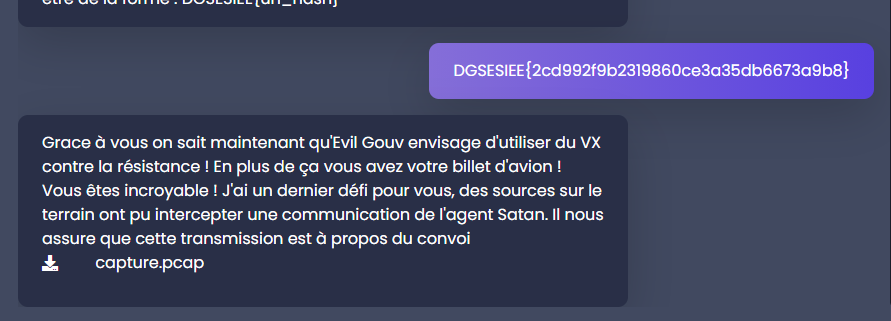
In this one I have to find a hidden communication, inside the pcap file.
And I found out that the messages are TLS encrypted.
I extracted the certificate from the handshake, and used Ganapati’s RsaCtfTool to get the private key.
This is working because the public key of the certificate (RSA key) is weak.
Wireshark is configurable to decrypt SSL when we give him a private key.
This is pretty easy. Go to 'Edit' -> 'Preferences'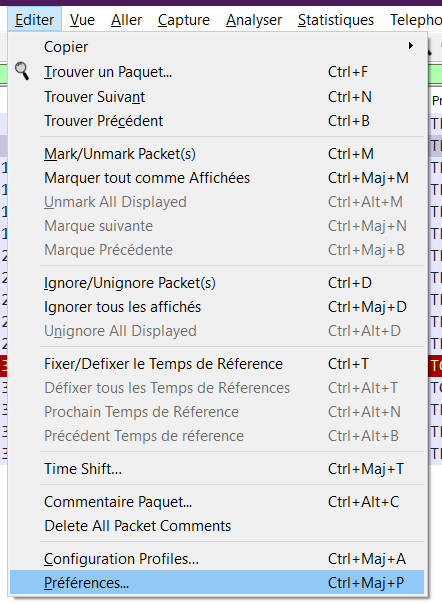
And in the ‘protocol’ section, find ‘TLS’ or ‘SSL’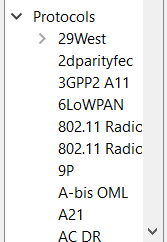
And import the private key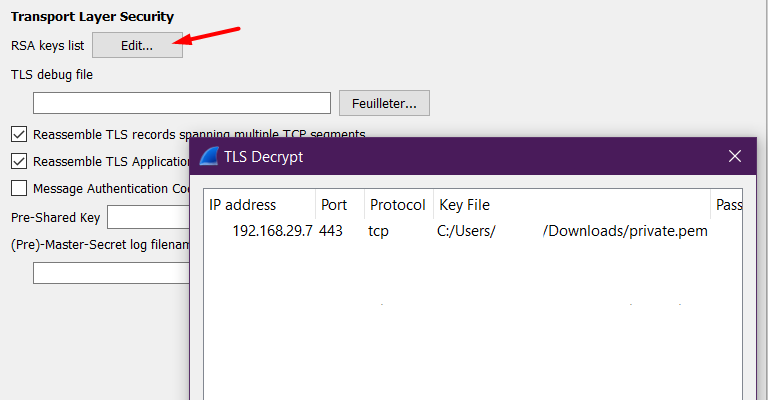
Victory is near.
I had to find the most relevant message (it was in red)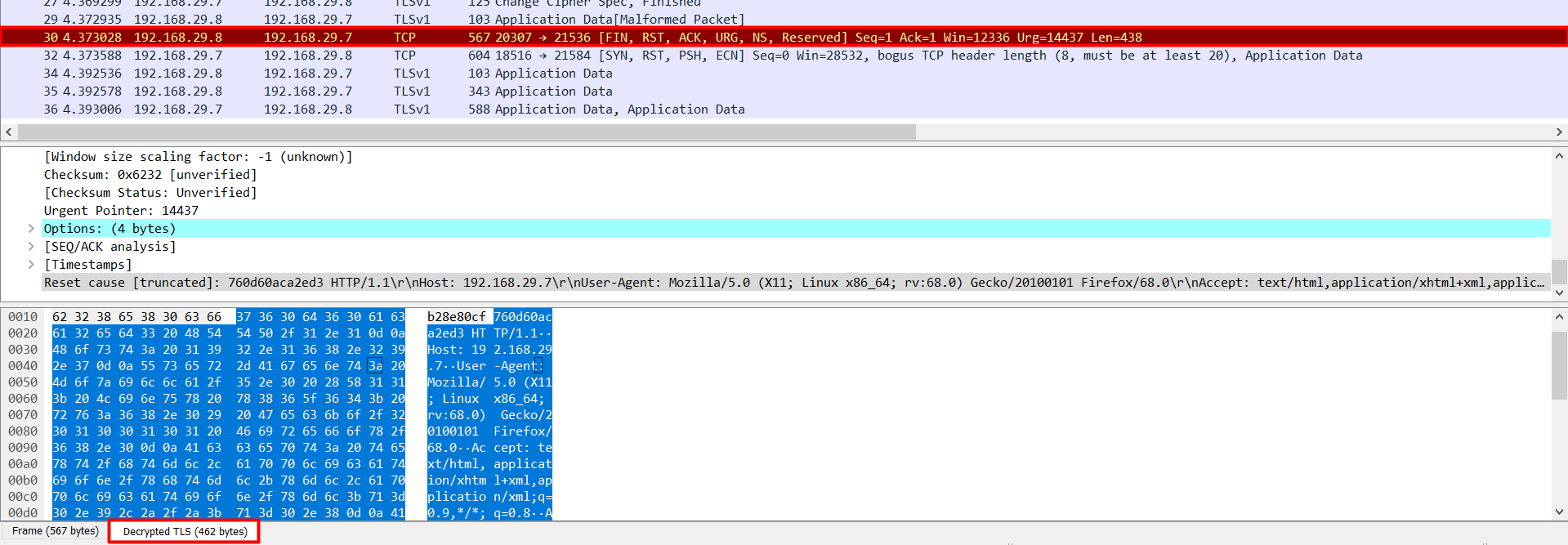
And get the TLS decrypted content :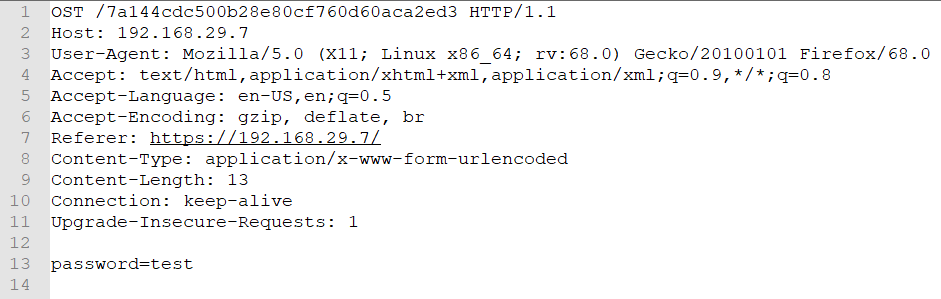
OST /7a144cdc500b28e80cf760d60aca2ed3 HTTP/1.1
Host: 192.168.29.7
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,/;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Referer: https://192.168.29.7/
Content-Type: application/x-www-form-urlencoded
Content-Length: 13
Connection: keep-alive
Upgrade-Insecure-Requests: 1
password=test
And there’s a hash, which looks like the previous directories we had.
Let’s put that after the URL: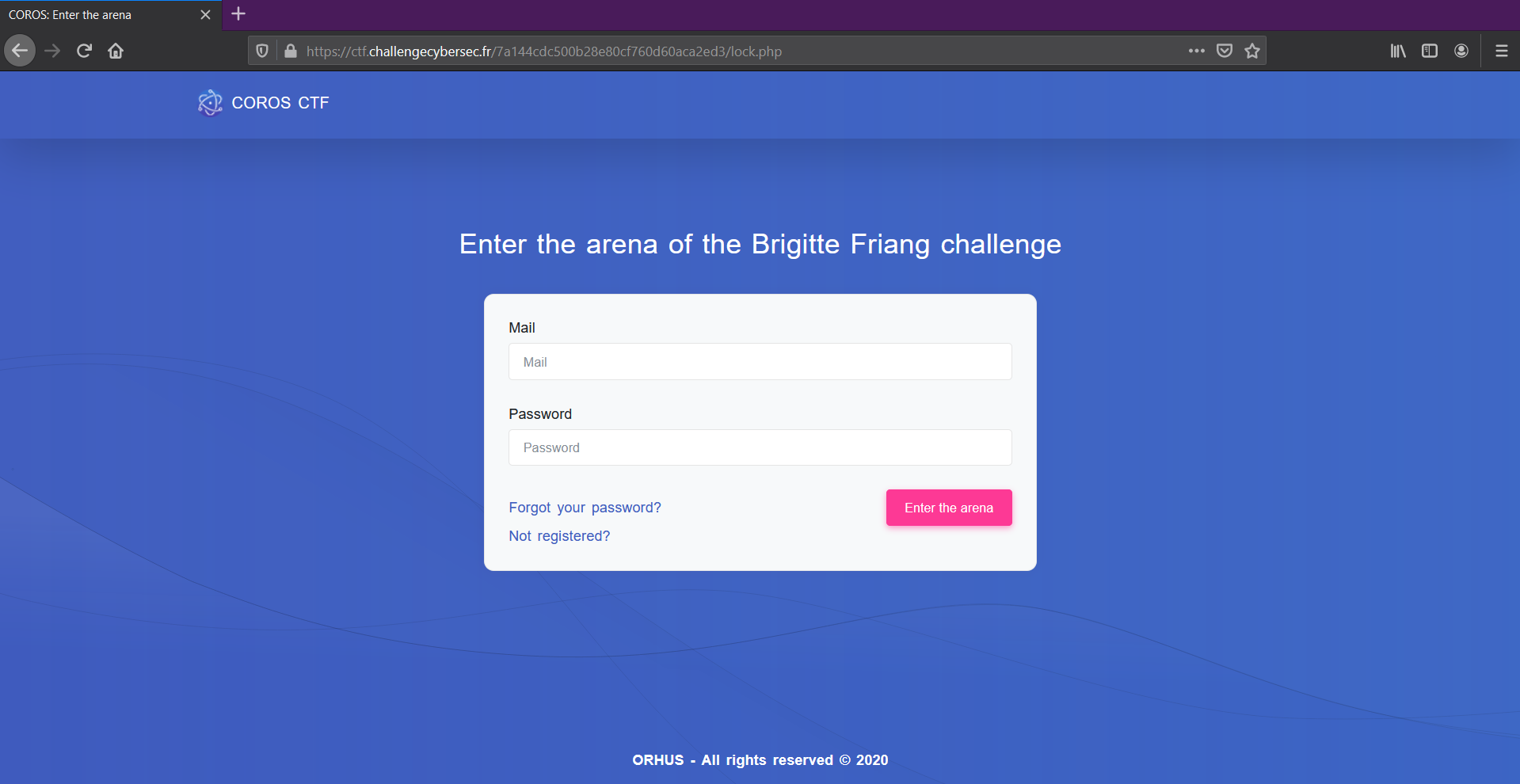
And that’s how I got my entry ticket to the CTF !
Blaise Pascal - Algorithms
I didn’t complete this challenge, but I wanna show you the first part.
Two files were given to me, an original, and an intercepted file, which is supposed to contain a hidden message.
the first thing we can see by comparing these two files is that, indeed, there are some additionnal characters in the intercepted file.
Original: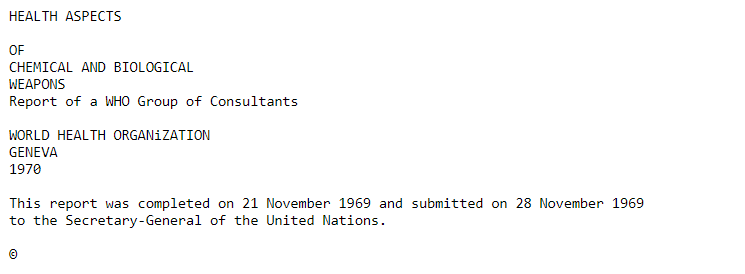
Intercepted: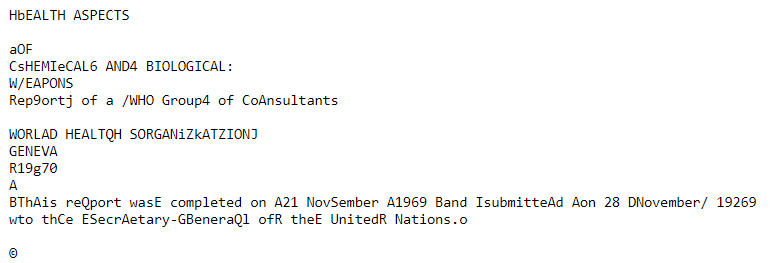
These files contain about 311762 characters, for the lightest, so i’m not gonna comapre them by hand.
So I created a python script :
# Import array, to use arrays
from array import array
# Open two files to compare
original = open("C:\\Users\\Cookie\\Downloads\\original.txt", "r")
intercepte = open("C:\\Users\\Cookie\\Downloads\\intercepte.txt", "r")
# Create two byte arrays
x_original = array('b')
x_intercepte = array('b')
x_result = array('b')
# Assign a file to each byte array
x_original.frombytes(original.read().encode())
x_intercepte.frombytes(intercepte.read().encode())
# Check each item in arrays, and compare them one by one
f = open("C:\\Users\\Cookie\\Downloads\\x_result_algo.txt", "a")
# For each character in the intercepted file, write extra caracter to file and delete it
for c in range(len(x_intercepte)):
while x_intercepte[c]!= x_original[c]:
f.write(chr(x_intercepte[c]))
x_intercepte.pop(c)
# Close the file
f.close()
# This script will end with a 'array index out of range' error, this is completely normal
I had a lot of issues with this, but finally everything is fine.
Some corrupted images I had :
(This one looks especially evil)
The result file contains base 64:
Which is an base64 encoded image: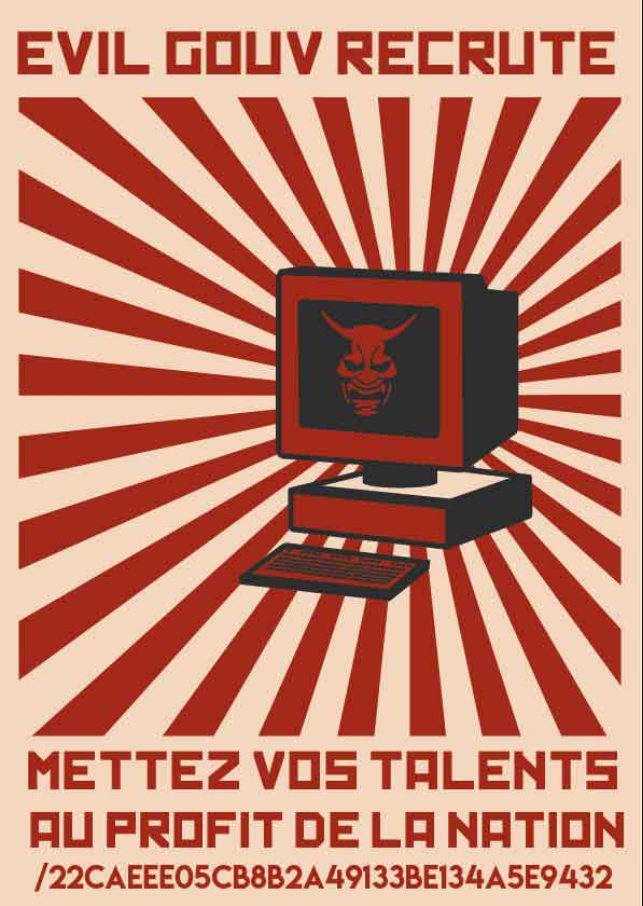
I that directory was a new webpage
And I stopped that challenge here.
Alphonse Bertillon - Forensics
An nginx log file was given to me.
And I had to find what the attackers IP is, he achieved to connect to the website, that’s all I knew.
So, i serched for multiple connection attempts, HTTP connection errors (such as 401)
But finally, it was in the user agent. The attacker used a browser called “Evil Browser”: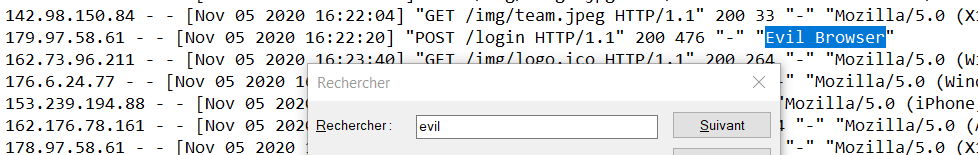
Here’s his IP address:179.97.58.61
Once given to Alphonse Bertillon, he gave me another file.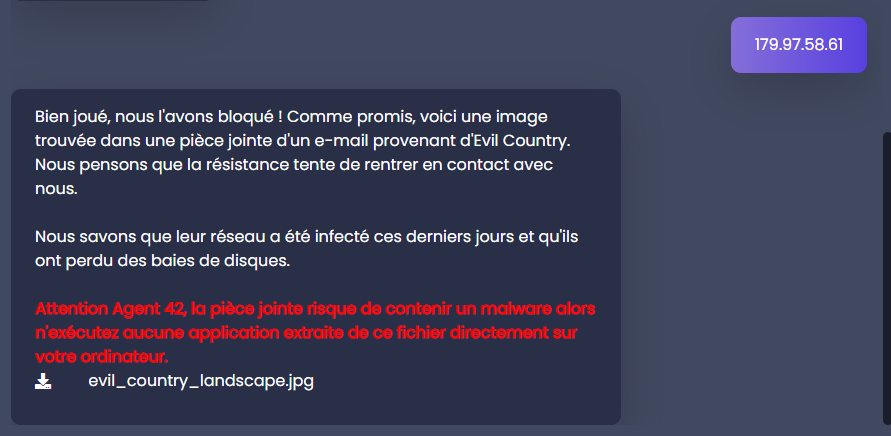
Apparently there can be malwares hidden into that file.
This file was an 303Mo heavy jpg image. But the picture quality is really poor.
So I simply used binwalk to see if theres anything uncommon. And yeah, indeed :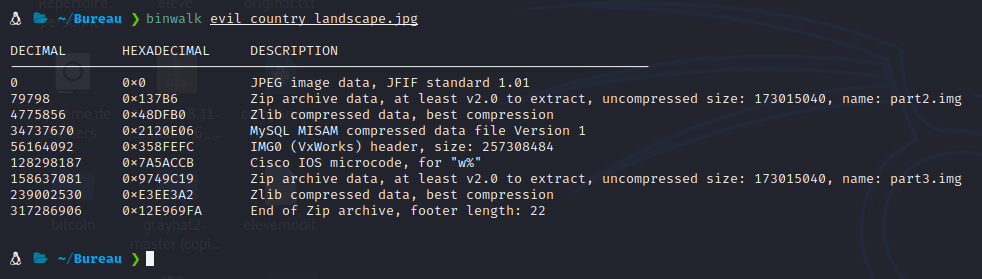
So let’s use the same tool to get these files.binwalk -e evil_country_landscape.jpg
I got 7 files,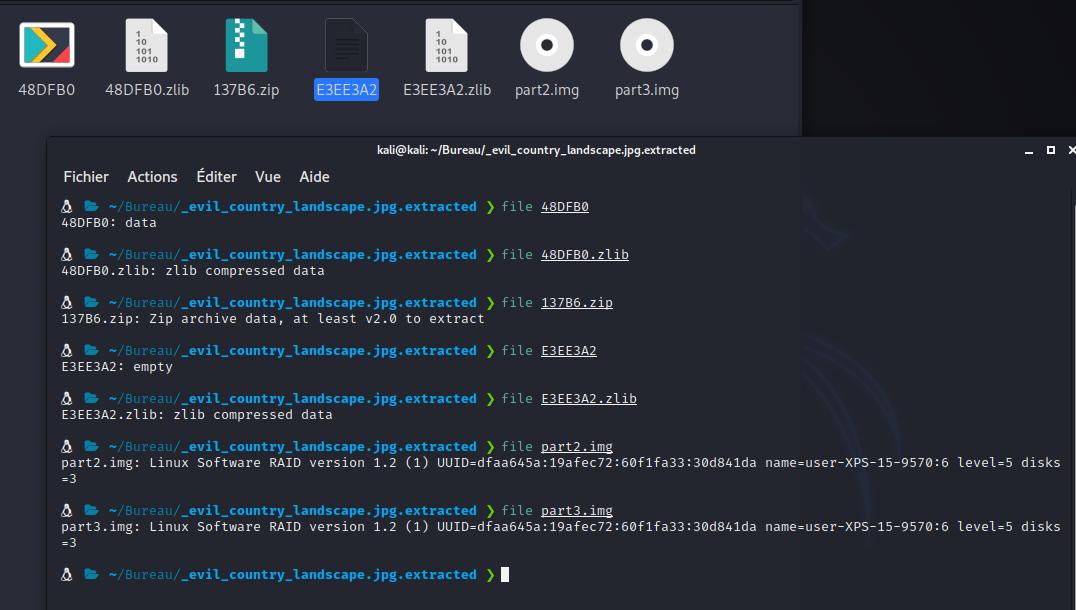
And I had not a Windows Virtual Machine at this moment, so this is where I left.